About listcrime
Listcrime is both a cybersecurity Threat Intelligence platform and a powerful suite of investigation tools.
It unites everyday users and cybersecurity experts to fight cybercrime through community knowledge, real-time alerts, and intelligent verification tools.
What our users actually care about
- “Is this website safe?”
- “Is this email compromised?”
- “Is this company legit?”
- “Am I being scammed?”
They want:
- simple answers
- confidence
- context they can understand
The platform also enables direct engagement with current and former federal, state, and local law enforcement professionals, allowing users to ask questions, share experiences, and receive informed guidance grounded in real-world investigative and operational expertise.
- Instantly verify who you’re dealing with online
- Don’t Guess. Investigate
- Check Anything Suspicious in Seconds
- Use Your Personal Listcrime AI Investigator™
- Expose Threats Before They Expose You
- Check anything suspicious in second
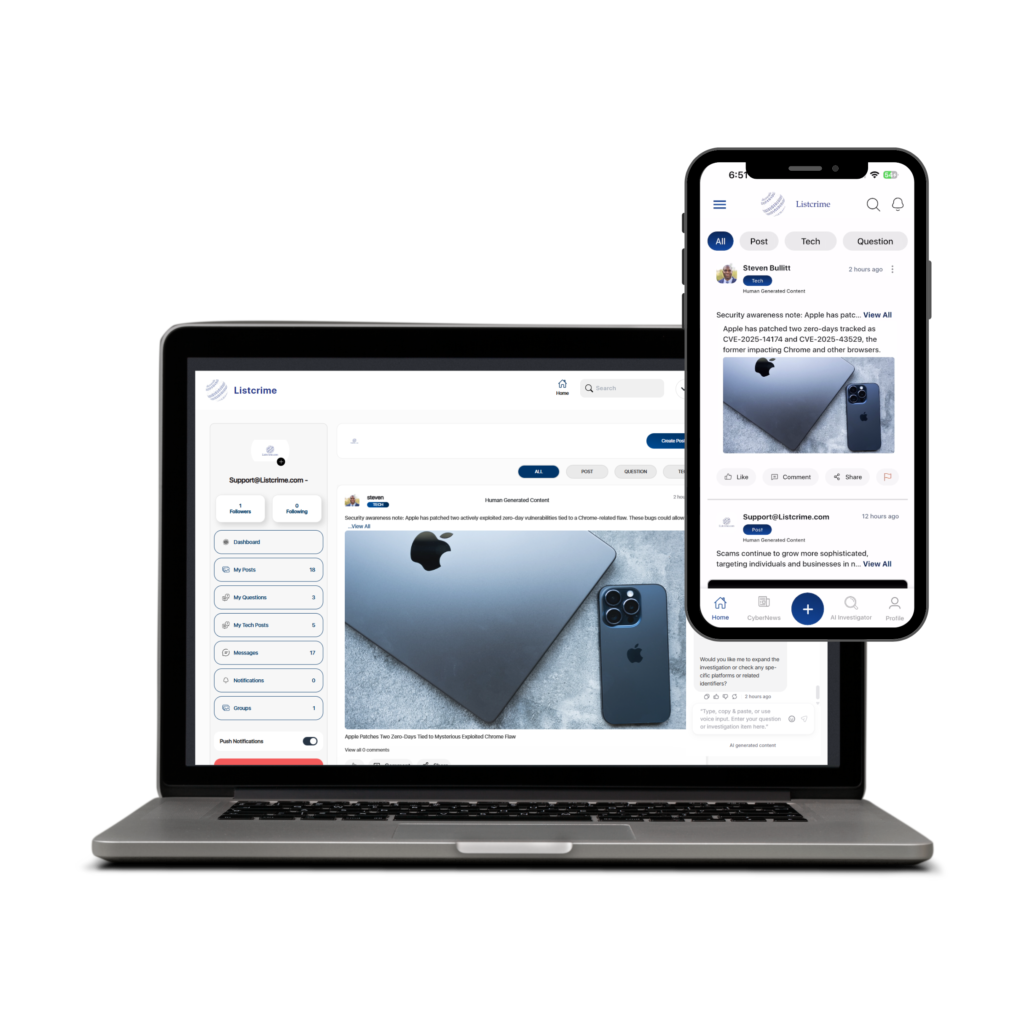
Listcrime supports both anonymous public participation and verified professional collaboration, with capabilities varying by trust tier.
DOWNLOAD THE APP HERE:
 Protection: “Before you click that link, check it on Listcrime.”
Protection: “Before you click that link, check it on Listcrime.”
 Empowerment: “Listcrime gives you the tools law enforcement uses.”
Empowerment: “Listcrime gives you the tools law enforcement uses.”
“Continue on Desktop” Web Portal Login
AI-Powered Investigation Engine
- Instantly analyze URLs, domains, emails, phone numbers, images, and identities
- Detect phishing, scams, and malicious behavior in seconds
- Built to uncover threats others miss
- AI Investigator™ (Your Digital Detective)
- Orchestrates specialized AI agents to investigate any threat
- Correlates data across multiple intelligence sources
- Provides clear, actionable results not just raw data
- Advanced Correlation Engine
- Connects domains, phone numbers, emails, and identities
- Reveals hidden relationships between threats
- Turns scattered data into meaningful intelligence
- Scan Anything, Anywhere
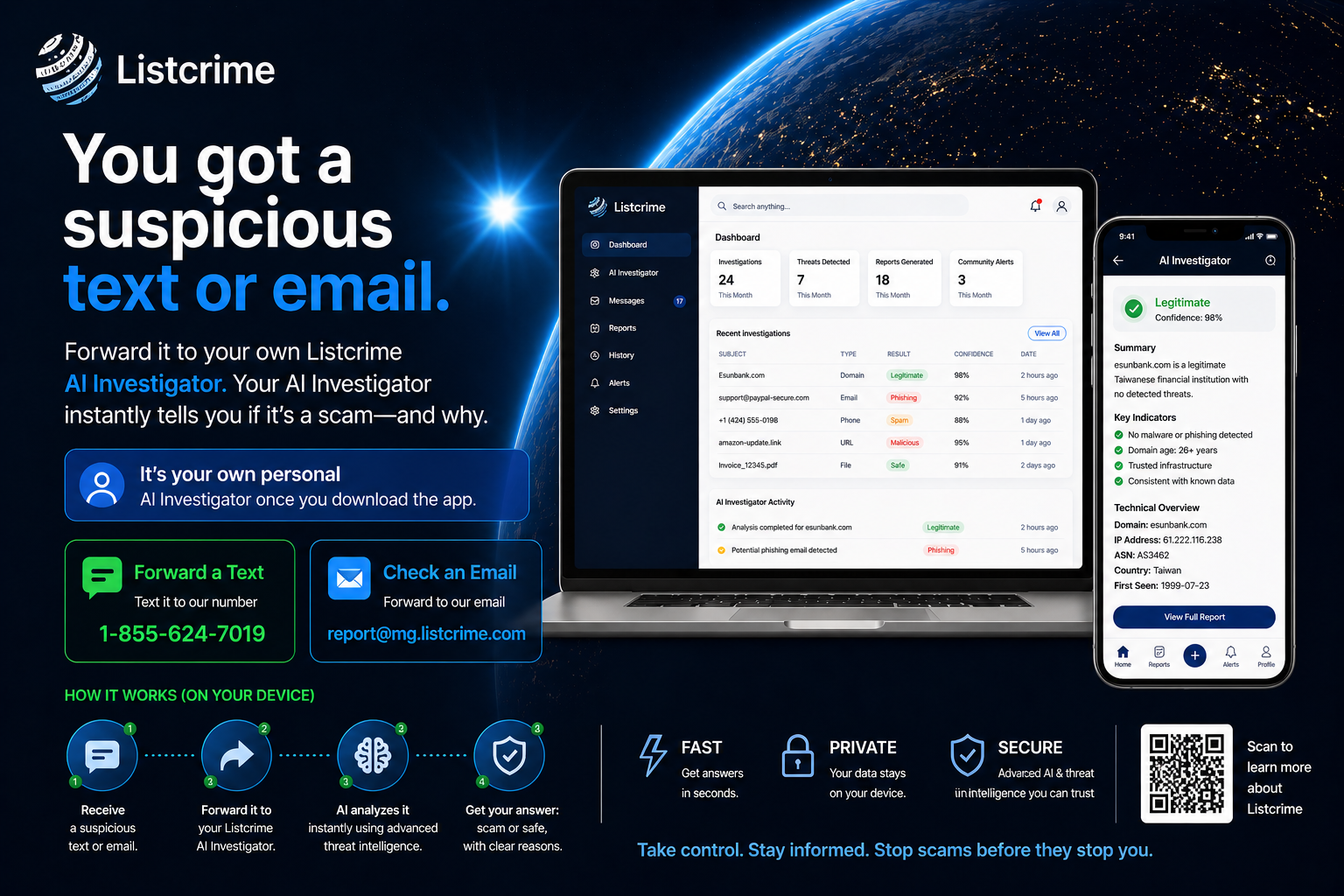
- Forward suspicious emails to report@listcrime.com
- Upload files, screenshots, and messages
- Forward Text messages directly into the App- Sign up here : https://listcrime.com/signup-page/
- For law enforcement, retail investigators, bank fraud teams, and financial institutions, the AI Investigator serves as a force-multiplier, automating time-consuming early-stage checks, consolidating open-source and threat intelligence, and providing fast, contextual insights that support informed investigative decisions.
- For everyday citizens, ListCrime provides a simple way to verify and validate suspicious phone numbers, emails, websites, domains, and business entities encountered in daily life. The goal is early awareness, education, and prevention—helping users make safer decisions before harm occurs.
- “Listcrime supports both anonymous public participation and verified professional collaboration. Capabilities vary by trust tier.”

Your own personal AI Investigator
A Borderless Solution
Cybercrime has no borders, and Listcrime is built to match that reality—connecting people worldwide to share verified intelligence and stop threats before they spread.
AI Investigator: Instantly check URLs, domains, businesses, job ads, texts, and emails in real time. Your personal AI agent analyzes threats on the spot so you can protect yourself and alert others.
See the Whole Picture
Listcrime unites everyday users and cyber experts, giving you the tools to verify suspicious messages, report scams, and stay protected—together.
AI Investigator: Use the AI Investigator to scan suspicious links, phone numbers, domains, or messages in seconds. Get immediate intelligence so you know what’s safe and what’s a scam.